Study what you love while living the life you dream of.
This qualification reflects the role of individuals in a variety of information and communications technology (ICT) roles who have significant experience in specialist technical skills, or managerial business and people management skills.
The course gives the opportunity for graduating students to work as an ICT specialist who has gained the skills and knowledge to plan, design, manage and monitor an enterprise information and communications technology network.
Individuals in these roles carry out complex tasks in a specialist field, working independently, leading a team or a strategic direction of a business. They apply their skills across a wide range of industries and business functions, or as a business owner (sole trader/contractor).
The skills required for these roles may include, but are not restricted to:
- Advanced data management information: creating, designing, and monitoring complex systems that store data, and optimising organisational knowledge management
- Cybersecurity: protecting sensitive data and information through security architecture, and developing disaster recovery and contingency plans
- Full-stack web development: building advanced user interfaces, developing representational state transfer application program interfaces (REST APIs) and designing user experience solutions
- Further programming: applying advanced ICT languages to maintain security and manage data
- IT strategy and organisational development: managing and communicating strategic ICT business solutions
- Systems development and analysis: modeling and testing data objects, data processes, and preferred ICT system solutions
- Telecommunications network engineering: managing logistics, organisational specifications, regulations and legislative requirements across network projects.
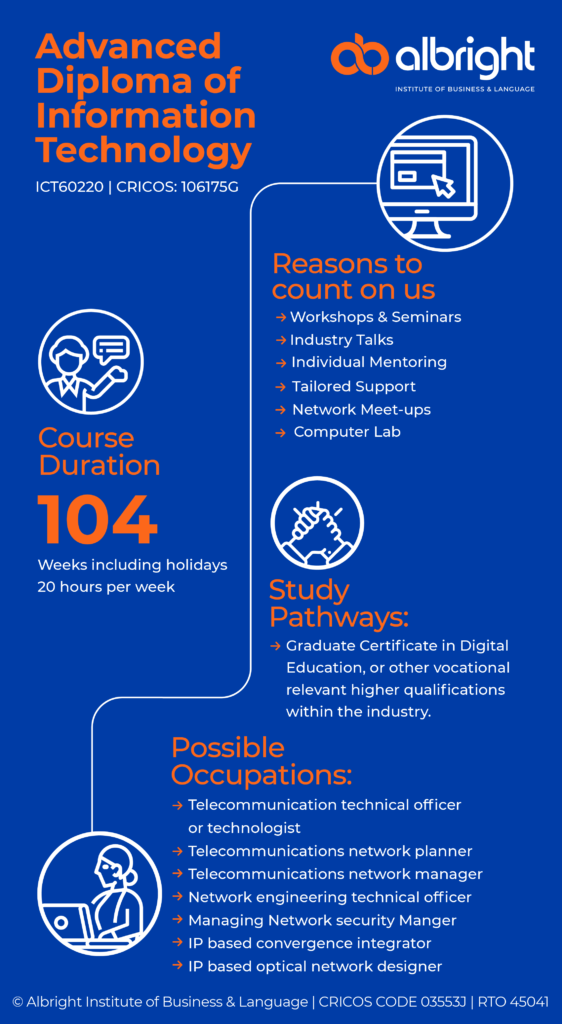
Graduate Certificate in Digital Education, or other vocational relevant higher qualifications within the industry.
- Telecommunication technical officer or technologist
- Telecommunications network planner
- Telecommunications network manager
- Network engineering technical officer
- Managing Network security Manger
- IP based convergence integrator
- IP based optical network designer
There are no formal entry requirements for this qualification, however, for enrolment in this course at Albright Institute a student must:
- Be 18 years of age at the time of commencement of the course
- Have successful completion of Australian Equivalent Year 12 qualification
- Have a valid Student Visa status OR will be granted the Student Visa which would allow them to study in Australia in Vocational AQF levels before the commencement of the course at Albright Institute.
- For Certificate III courses:
Have a valid IELTS score of 5.5 Bands OR PTE score of 42 OR Cambridge score B2 OR TOEFL iBT 46 OR its equivalent (Completed a minimum 10-weeks General English Course of Upper-Intermediate Level)- Within the last 3 Calendar Years OR Completed Australian Qualification minimum AQF Level from Level 3 (Certificate 3) to Advanced Diploma AQF Level 6 OR Successful completion of Australian Equivalent Year 11 qualification – Within the last 3 Calendar Years; - Have a valid IELTS score of 5.5 Bands OR PTE score of 42 OR Cambridge score 162 OR TOEFL iBT 46 OR its equivalent (Completed a minimum 10-weeks General English Course of Upper-Intermediate Level)- Within the last 3 Calendar Years OR Completed Australian Qualification minimum from AQF Level 3 (Certificate 3) to Advanced Diploma AQF Level 6 OR Successful completion of Australian Equivalent Year 12 qualification – Within the last 3 Calendar Years;
- Complete the Albright Language, Literacy & Numeracy (LLN) test
- Have basic computer and MS Office skills (Word, Excel and Power Point)
- Satisfy Pre-Training Review (PTR) Assessment requirement
- Total number of units = 16
- 6 core units plus
- 10 elective units
- 104 Weeks Including holidays
- 20 hours per week
Melbourne, Sydney, Adelaide & Brisbane
Core Units
- BSBCRT611 Apply critical thinking for complex problem solving
- BSBTWK502 Manage team effectiveness
- BSBXCS402 Promote workplace cyber security awareness and best practices
- ICTICT608 Interact with clients on a business level
- ICTICT618 Manage IP, ethics and privacy in ICT environments
- ICTSAD609 Plan and monitor business analysis activities in an ICT environment
Elective units:
Group G – Telecommunications network engineering specialisation
- ICTNPL413 Evaluate networking regulations and legislation for the telecommunications industry
- ICTNWK612 Plan and manage troubleshooting advanced integrated IP networks
- ICTPMG613 Manage ICT project planning
- ICTTEN615 Manage network traffic
- ICTTEN622 Produce ICT network architecture designs
Telecommunications Network Engineering – General
- BSBLDR523 Lead and manage effective workplace relationships
- BSBPMG530 Manage project scope
- BSBPMG430 Undertake project work
Telecommunications Network Engineering – Networking
- ICTNWK546 Manage network security
Network Security
- ICTNWK540 Design, build and test network servers
Typical Timetable Block*
AM Schedule Block | Start | End |
Period 1 | 9:00 AM | 12:30 PM |
Break | 12:30 PM | 1:00 PM |
Period 2 | 1:00 PM | 4:30 PM |
PM Schedule Block | Start | End |
Period 1 | 2:00 PM | 5:30 PM |
Break | 5:30 PM | 6:00 PM |
Period 2 | 6:00 PM | 9:30 PM |
Compulsory Training Hours:
**Timetables specific to each course or cohort are released before the start of the commencement week and updated at the beginning of each term.
|
During the training sessions, participants are required to bring their own device in order to complete work simulated activities in classroom.
BYOD minimum requirements are as follows:
- Operating System: Windows 8 Home Edition or later
- Processor: Intel Core i3 / AMD 2.0 Ghz or better
- RAM: Minimum 4 GB, recommended 8GB
- Hard Drive: 128GB SSD (256GB SSD recommended if not using Cloud storage) Display: 13 inch full HD (1920 x 1080) with a built-in webcam
- WiFi: 802.1x compliant
- USB Headsets with microphone
- Device must be fully charged
BYOD stands for bring your own device, and the most commonly accepted BYOD meaning is when students use their own personal devices to connect to the LMS and access what they need to do their tasks and attend classes. This includes data and information that could be potentially sensitive or confidential, so here are some tips to ensure you maximize the security!
One of the most common best practices listed in a BYOD policy is for users to have installed some kind of security software on their personal devices. This includes antivirus software, mobile device management (MDM) software, and unified endpoint management (UEM) software.
✔ Try not to leave your device unattended.
✔ Ensure someone is looking it after if you are briefly absent.
✔ Save your work on an external portable memory.
✔ Bring your device charger: AIBL will ensure to provide power points along all facilities in campus for your convenience.
FAQs
Why is a BYOD policy important?
Enables students to bring your own device that typically already know how to use it and avoid complex security protocols.
What are the best practices of BYOD security?
Use strong passwords, determine the kinds of sensitive data, place mobile security tools on devices, choose time-based lockout features, and determine how to wipe sensitive information off the user’s device.
What is a BYOD example?
The devices used for BYOD could include tablets, personal computers & laptops

Contact Us
Want more information about our courses?
Submit your contact details here and we will get back to you as soon as possible.

